Technology is evolving at a pace that makes yesterday’s breakthroughs feel outdated almost overnight. Whether you’re trying to understand AI and machine learning, explore the real risks behind quantum computing, or simply troubleshoot a persistent device issue, you’re here because you want clarity—not jargon, not hype, and not half-explained concepts.
This article is designed to meet that need directly. We break down complex technical subjects into practical, structured insights you can actually use. From a clear cybersecurity fundamentals overview to deeper analysis of emerging threats and advanced computing shifts, every section focuses on what matters most: how the technology works, why it matters, and what it means for you.
To ensure accuracy and relevance, the content draws on established technical research, current industry standards, and real-world implementation practices across cybersecurity, AI systems, and modern computing infrastructure. The goal isn’t just to inform—it’s to equip you with a reliable foundation you can build on.
If you’re looking for straightforward explanations, expert-level context, and actionable understanding of today’s core tech concepts, you’re in the right place.
Last year, I woke up to dozens of password reset emails. My bank account was fine, but my streaming subscription wasn’t. That small scare forced me to confront a hard truth: digital security is survival.
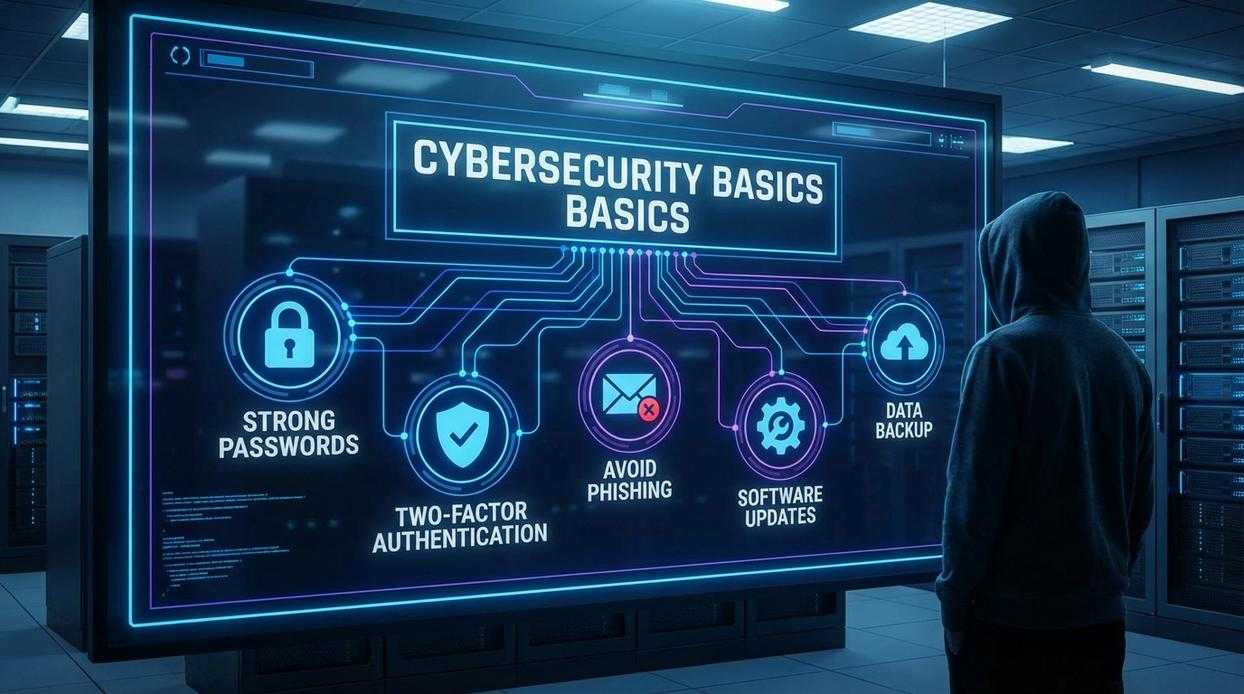
In this cybersecurity fundamentals overview, think of protection like locking your front door.
Strong passwords are deadbolts.
Multi-factor authentication is the alarm system.
Regular updates patch broken windows.
Some argue breaches only hit big companies, citing headlines about Fortune 500 hacks. Yet Verizon’s 2023 DBIR found 74% of breaches involve human error. That’s us.
Staying secure isn’t paranoia; it’s practical self-defense online.
The Three Pillars of Information Security: The CIA Triad
At the heart of every cybersecurity fundamentals overview is the CIA Triad—Confidentiality, Integrity, and Availability. These three principles form the backbone of modern security architecture (yes, even the systems quietly running your favorite streaming app).
Confidentiality is about keeping secrets secret. It ensures sensitive information—like passwords, financial records, and private messages—remains accessible only to authorized users. Without confidentiality, your online banking login could be exposed to attackers in seconds. Encryption, which transforms readable data into coded text, is the primary defense here. Even if intercepted, encrypted data is useless without the decryption key. Some argue strong encryption slows performance. In reality, modern encryption standards like AES-256 are optimized for both speed and security (NIST).
Integrity guarantees that data hasn’t been altered or tampered with. Imagine a bank transaction changing from $100 to $10,000 mid-transfer. Hashing creates a unique fingerprint of data, while digital signatures verify authenticity. Critics sometimes claim internal systems are “safe enough.” Yet insider threats account for 34% of breaches (Verizon DBIR), proving verification is non-negotiable.
Availability ensures systems and data are accessible when needed. A Denial-of-Service (DoS) attack floods a system with traffic, making it unavailable to legitimate users. Backups and system redundancy—duplicate systems running in parallel—help maintain uptime. Pro tip: test backups regularly; untested backups are just wishful thinking.
• Confidentiality protects privacy
• Integrity preserves trust
• Availability ensures continuity
Together, these pillars don’t just protect data—they protect reputations, revenue, and reliability.
Know Your Enemy: Common Cyber Threats and Attack Vectors
Understanding cyber threats starts with a solid cybersecurity fundamentals overview. You can’t defend what you don’t recognize.
Malware
Malware (malicious software) is any program designed to harm, exploit, or disrupt systems. Common types include:
- Viruses – Attach to legitimate files and spread when executed.
- Ransomware – Encrypts your data and demands payment for release.
- Spyware – Secretly monitors activity and steals information.
Infection often happens through unsafe downloads, email attachments, or compromised websites. Pro tip: Always verify file sources and enable automatic system updates—many attacks exploit outdated software (CISA).
Phishing
Phishing is a social engineering tactic—manipulating people into giving up sensitive data. Attackers send emails that appear legitimate, such as:
“Your bank account has been locked. Click here to verify.”
The link leads to a fake login page that captures your credentials.
Actionable steps:
- Check the sender’s email domain carefully.
- Hover over links before clicking.
- Never share passwords via email.
Even tech-savvy users fall for well-crafted scams (yes, even the “I swear this looked real” moments).
Denial-of-Service (DoS) Attacks
A Denial-of-Service (DoS) attack floods a server with traffic until it crashes, targeting the Availability pillar of security. Think of it like 10,000 fake customers blocking a store entrance.
Mitigation tip: Use traffic filtering and rate limiting. Strong devops best practices for faster and safer deployments help teams respond quickly to traffic anomalies.
Man-in-the-Middle (MitM) Attacks
In a MitM attack, someone secretly intercepts communication between two parties. Unsecured public Wi-Fi is a classic example. An attacker can capture login credentials or modify data in transit.
Protect yourself:
- Use HTTPS websites only.
- Avoid sensitive transactions on public Wi-Fi.
- Use a reputable VPN when traveling.
Cybersecurity isn’t paranoia—it’s preparation.
Your First Line of Defense: Practical Cybersecurity Measures
Strong Authentication starts with moving beyond basic passwords. Even complex passwords can be cracked—Verizon’s 2023 Data Breach Investigations Report found that over 80% of breaches involve stolen or weak credentials (Verizon DBIR, 2023). That’s why password managers matter. They generate and store long, unique passwords for every account (yes, every single one). Pair that with Multi-Factor Authentication (MFA)—a security method requiring two or more verification factors—and you dramatically reduce risk. Microsoft reports MFA can block over 99.9% of account compromise attacks (Microsoft Security Blog). In other words, MFA is no longer optional; it’s the baseline.
The Principle of Least Privilege in Action
Next, consider the Principle of Least Privilege (PoLP). This means giving users only the minimum access required to perform their tasks. If a marketing intern doesn’t need financial records, they shouldn’t have access. Why? Because if their account is compromised, the attacker’s reach is limited. It’s like giving someone a house key but not the garage remote (small access, smaller fallout). This approach is a cornerstone of any cybersecurity fundamentals overview.
Meanwhile, Software Patching and Updates close known security gaps. The Equifax breach in 2017 stemmed from an unpatched vulnerability—affecting 147 million people (FTC report). Updates aren’t cosmetic; they fix exploitable flaws. Timely patching of operating systems and apps is critical.
Finally, develop a Security Mindset. Pause before clicking. Verify email senders. Hover over links. Cybersecurity tools help—but informed skepticism is your strongest defense (and attackers count on you skipping that second look).
Building a Resilient Digital Future
You now understand the pillars of Confidentiality, Integrity, and Availability—the cybersecurity fundamentals overview that keeps systems trustworthy. The digital world can feel chaotic and dangerous, yet phishing emails, ransomware, and data leaks all succeed the same way: they exploit cracks in those basics. When credentials are reused, Confidentiality fails. When patches are ignored, Integrity erodes. When backups are missing, Availability disappears (and suddenly “I’ll do it later” becomes famous last words).
The path forward is practical. Use strong, unique passwords stored in a manager. Turn on multi-factor authentication. Install updates promptly. Encrypt devices. These habits may sound simple, but consistency is what turns them into a resilient shield.
What’s next? Audit your accounts, review recovery options, and map your critical data flows. Security is not a one-time setup—it’s an ongoing discipline. Start today by enabling MFA on your important account. Future you will be grateful.
Strengthen Your Security Before It’s Too Late
You came here looking for clarity on cybersecurity fundamentals overview, and now you have a practical understanding of the core principles that keep systems, data, and devices secure. From threat awareness to layered defenses and proactive monitoring, you’ve seen how foundational security practices directly reduce risk.
The reality is this: cyber threats aren’t slowing down. Attack surfaces are expanding, AI-driven attacks are getting smarter, and even a single overlooked vulnerability can lead to costly downtime, data loss, or reputational damage. Ignoring the fundamentals is no longer an option.
The good news? Mastering and consistently applying these core cybersecurity principles puts you back in control. When you prioritize strong authentication, regular updates, network segmentation, and user awareness, you dramatically reduce your exposure.
Now it’s time to act. Review your current security posture, identify weak points, and implement the safeguards you’ve learned today. If you want trusted, expert-backed insights on emerging threats, AI-driven risks, and practical defense strategies, explore our in-depth resources and stay ahead of evolving cyber risks. Don’t wait for a breach to expose the gaps—strengthen your defenses now.
